Mobile ad fraud: how it works, why it happens, and how to stop it
Lotfi Zazoun
•
Business Operations
•
March 17, 2026
•
7 min read
This guide explains what mobile ad fraud is, why it continues to grow, the six most common fraud techniques affecting app marketers, and how Tapper detects and blocks them to protect campaign performance.

What is mobile ad fraud?
Mobile ad fraud is the deliberate manipulation of mobile advertising systems to steal from advertiser budgets. Fraudsters exploit the mechanics of ad attribution, impressions, clicks, installs, and post-install events, to generate payments for activity that never genuinely occurred.
The forms it takes vary. Some fraudsters stuff multiple ads into a single pixel or place ads deliberately out of view to register impressions that no real user ever saw. Others go further, fabricating entire install events using bots or device farms, or manipulating post-install signals to poison the data that drives bidding decisions.
Why does it keep happening?
The financial incentive is straightforward: mobile advertising fraud is a fast, low-risk way to extract money from large budgets. Two forces keep it alive. Mobile technology evolves continuously, and fraud techniques evolve alongside it. At the same time, accountability across the supply chain remains fragmented, no single party feels fully responsible, so most do nothing.
Solving this at scale requires industry-wide coordination. Progress is happening, but it depends on continued development in detection technology, clearer standards, and honest acknowledgment of how widespread the problem is.
Six types of mobile ad fraud marketers need to know
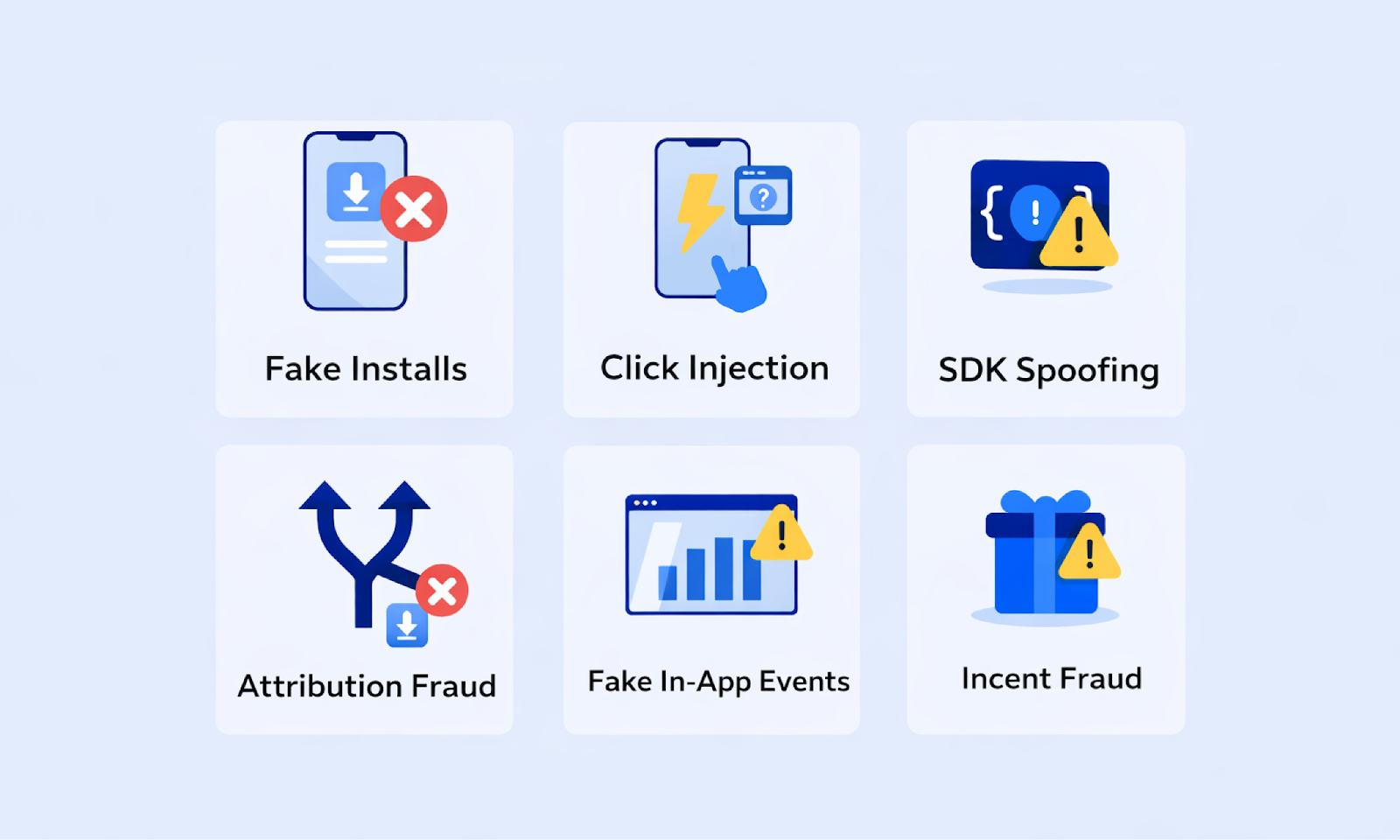
1. Fake installs
Bot-generated or incentivised installs that never come from real users. They waste budget, inflate CPI, and make acquisition data unreliable. Marketers end up optimising toward sources that produce nothing of value.
2. Click injection
Fraudsters publish Android apps that listen for install broadcasts. The moment another app is about to complete installation on a device, they fire a fake click to hijack the attribution credit. Without prevention in place, the fraudster receives credit for an install they had nothing to do with.
3. Install spoofing
Also known as traffic spoofing or replay attacks. Install events are simulated entirely without a real device or user, they are invisible to standard MMP checks. The data looks legitimate on the surface, but the installs never happened.
4. Attribution fraud
Manipulated attribution signals that credit fraudulent sources with real conversions the advertiser legitimately earned. The install or event is real, but the credit goes to the wrong place, distorting ROI reporting and channel performance data.
5. Fake in-app events
Bulk invalid post-install events injected after a real or fake install. These corrupt the optimisation signals that automated bidding systems rely on, causing algorithms to chase the wrong users and driving up costs with no return.
6. Incent fraud
Low-quality users who are paid or incentivised to install an app with no genuine intent to use it. Installs go up, but lifetime value collapses. These users distort retention metrics and degrade the quality of lookalike audiences built from install data.
What does ad fraud actually cost?
Digital ad fraud will cost advertisers an estimated $136 billion this year globally and a significant share of that loss comes from mobile ad fraud.
For mobile app marketers, unchecked fraud degrades attribution data over time, causing budget to flow toward channels producing little or no real user activity. The result is skewed metrics, wasted spend, and campaigns optimised against a false picture of performance.
How Tapper stops mobile ad fraud
Tapper detects and blocks the full range of mobile acquisition fraud vectors, not just invalid clicks. Its fraud prevention works at the point of attribution, blocking fraudulent traffic before it enters your dataset. Every install event and post-install signal is analyzed in real time, scanned for anomalies, and assessed against known fraud patterns. The focus on individual events keeps false positives out and ensures clean data flows through to your reporting.
Tapper tackles each major fraud type with a dedicated solution:
| Fraud type | Tapper’s solution | How it works |
|---|---|---|
| Fake installs | Install verification | Bot-generated and incentivised installs are identified before they register as valid conversions. Tapper cross-checks install signals against device and behavioral data to confirm that each install originated from a real user, blocking inflated CPI figures and wasted budget at the source. |
| Click injection | Click injection filter | Deterministic timestamps are used to detect and block clicks fired at install time to hijack attribution. If a click arrives suspiciously close to an install event in a way that matches known injection patterns, it is rejected before credit is assigned. |
| Install spoofing | Install validation layer | Each install is assigned a unique digital signature through multi-layered encryption. This makes it impossible for fraudsters to replicate or replay install data from real devices, ensuring that only genuine installs pass through. |
| Attribution fraud | Real-time attribution validation | Tapper cross-references attribution signals against verified engagement data to identify manipulated conversion paths. When a fraudulent source attempts to claim credit for a conversion the advertiser legitimately earned, the signal is flagged and the attribution is corrected before it affects reporting. |
| Fake in-app events | Event integrity monitoring | Post-install events are validated in real time to filter out bulk invalid signals injected after installation. By screening out fabricated in-app activity, Tapper protects the optimisation data that automated bidding systems rely on, preventing algorithms from being trained on fraudulent behavior. |
| Incent fraud | User quality scoring | Not all installs that pass technical checks are worth keeping. Tapper evaluates post-install behavior patterns to identify users who were incentivised to install with no genuine intent to engage. These installs are flagged so they do not contaminate retention metrics, bidding models, or lookalike audience data. |
With Tapper, campaign planning and performance reviews are based on accurate data, not numbers inflated by bot activity, hijacked installs, or corrupted in-app events. If you want to protect your ad spend and make decisions based on data you can trust, Tapper’s fraud prevention suite is built to do exactly that.
See how Tapper protects mobile acquisition campaigns end to end at tapper.ai/mobile.
Stop Paying for Fake Traffic
Run a 30-day Tapper trial to set your baseline CPA, block invalid traffic in real time, and receive a final report comparing your CPA before and after protection.
Get a demo